Let's Talk ➔
Achieve objectives reliably. Safeguard your organization.
Changing challenges. Growing risks.
The Key Questions
Large organizations must manage evolving risks across diverse business units and geographies while combating fragmented data that obscures a unified, transparent view for all stakeholders. In the digital age, this entails prioritizing cybersecurity measures and robust data protection protocols to safeguard sensitive information from unauthorized access and cyber threats.
They grapple with a rapidly changing regulatory environment and the surge of digital transactions, necessitating agile governance, risk, and compliance (GRC) strategies. With increased focus on cybersecurity regulations such as NIS Directive, EU Cybersecurity Act or GDPR, organizations must ensure their GRC framework adequately addresses these requirements while securing all digital exchanges against vulnerabilities.
Additionally, instilling a pervasive compliance culture throughout all levels of an organization remains a formidable challenge in ensuring holistic and effective GRC. This includes training employees on cybersecurity best practices, promoting awareness about potential threats, and enforcing policies that support data integrity and confidentiality. Achieving this not only helps in compliance but also builds trust with customers and stakeholders by demonstrating a commitment to protecting their data.
- // Smart Technology & Platforms
- // Production & Operations
- // Service Operations
- // Internet of Things

How to provide a risk-based, risk-informed or risk-adjusted approach to management?
Click to Flip
Ready access not only to KPIs, but also to risk, control and audit information, i.e. a holistic picture in decision making is the key for effectively tracking and achieving the strategies originally set out.

How to stay ahead of regulations and foster application security and regulatory compliance while addressing the challenges posed by threat actors.
Click to Flip
By providing not only native integration with SAP landscape for Cybersecurity and IAM solutions but also thanks to integration with SAP GRC to speed-up and rationalize the compliance activities and reporting.

How do we achieve objectives more reliably?
Click to Flip
Continuous automated monitoring will not only reduce cost of doing GRC, but improve assurance and business outcome: help employees to avoid (costly) mistakes, and serve as guardrails to more reliably achieve objectives.

How do you keep up with digital transformation and the resulting big data?
Click to Flip
Direct integration to backend systems and leveraging the information there will allow for automated monitoring of the full population of all transactions – in near real-time.

How do we focus our GRC activities on those objects that really matter, and how can risk, controls, and internal audit functions be real business advisors?
Click to Flip
A risk registry with current risk information will allow to risk-prioritize activities, and an integrated platform ensures consistent risk, control, compliance, and audit information, avoids duplicate activities and provides a single source of truth, thereby streamlining efficiency and effectiveness of business processes.

How do IT & Cybersecurity specialists get the management attention for cybersecurity risks?
Click to Flip
Use one single, coherent, consistent enterprise-wide risk framework that reports all enterprise risks using the same methodology, measurements and standards. This approach ensures that cybersecurity risks become visible and comparable with other enterprise risks, making it easier for management to understand, prioritize and act on them.
SAP GRC - Cybersecurity & Access Governance
Protect your critical business processes and data
It is well known that the challenges for cybersecurity are very diverse and are increasing. SAP have a broad range of market-leading solutions which can answer many of these challenges and if your vital data is stored in an SAP ERP, it is even more relevant to consider the solutions which were designed with that ERP in mind.
Example of a Cyber Attack Blocked with SAP Security Solutions
Anatomy of a cyber-attack neutralized with SAP Security solutions: SAP ETD, SAP UI Masking, IAM solutions.
Our Vision and Approach
// Safeguard your organization
// Achieve objectives of the organization more reliably
SAP solutions for GRC & Security deliver on this vision through a holistic approach.
Integration across a unified platform streamlines risk management, controls, audit, and compliance processes.
Integration to the backend, leveraging information from various backend systems, SAP delivers near real-time risk and control monitoring insights.
The Approach and Outcome
The five phases can be broken down to detailed activities
⍟ Analyze business & digital strategy, operating model, organization, and vision*
⍟ Analyze business model & organization
⍟ Analyze as-is enterprise architecture
⍟ Create as-is system list
⍟ Run Process Discovery (Readiness Check)
⍟ Define life science to-be business processes
⍟ Identify IT applications and innovations
⍟ Design target life science application architecture
⍟ Integrate life science architecture into overall IT landscape
⍟ Define transformation roadmap
⍟ Define roll-out plan
⍟ Define & evaluate Implementation Strategy
⍟ Conduct risk assessment
⍟ Conduct change impact analysis
⍟ Estimate costs, quantify value, calculate business case
⍟ Provide transformation guidance
⍟ Provide approach, policies, principles, standards, key success factors
⍟ Implementation program organization, roles & responsibilities
Typical project plan showing main service phases
Service Preparation Phase
~1-3 Weeks
✪ Prepare for service delivery (refine scope and approach, service schedule and deliverables)
✪ Mobilize SAP consultants and customer stakeholders
✪ Prepare and execute kick-off meeting
✪ Confirm final scope and schedule service delivery workshops
Service Delivery Phase
~16-48 Weeks
✪ Perform activities as required (such as workshops, interviews, design, planning, justification, evaluation and documentation) for building blocks
- Discover
- Design
- Plan
- Justify*
- Transform and scale*
✪ Manage project (performed on a permanent basis as required during the execution of the service)
* Scope option Extended only
Service Closure Phase
~1-2 Weeks
✪ Complete service documentation
✪ Perform final presentation: Present and discuss results, propose follow-up activities and next steps
✪ Hand over deliverables, and close service
Our SAP GRC Portfolio
SAP’s GRC solutions enhance core business processes by seamlessly integrating governance, risk management, control, compliance, audit, and security processes. Organizations typically begin by assessing their risk exposure (top).
Many aim to implement the Three Lines Model, as recommended by the Institute of Internal Auditors and leading advisory firms, to align risk management with controls, compliance, and internal audit processes (right).
Security is another critical area, encompassing user access controls, data protection, and cybersecurity measures (left).
Additionally, organizations involved in cross-border trade require efficient import/export capabilities that ensure compliance with international regulations (bottom)."
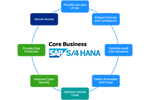
Our SAP GRC Security Vision
The below visual shows our SAP GRC portfolio in greater details, with all the components available.
Enterprise Risk, Controls & Compliance and Audit (Three Lines)
Identity & Access Gov.
Cyber Security, Data Protection and Privacy
International Trade Mgmt

Provide one view of risk

Embed Controls + Compliance

Anomaly + Fraud Detection

Optimize Audit + Assurance

Secure Access

Data Protection

Cyber Security

Optimize International Trade
SAP S/4HANA Cloud for financial Three Lines of Defense
SAP Access Control
SAP UI Data Protection, Masking + Logging
SAP Enterprise Threat Detection
International Trade Mgmt (core S/4HANA capability)
SAP Risk Mgmt
SAP Process Control
SAP Business Integrity Screening
SAP Audit Management
SAP Identity Access Governance
SAP Data Custodian, Key Mgmt Svc
SAP Code Vulnerability Analyzer
SAP Global Trade Services
SAP Risk and Assurance Management
SAP Secure Login Service for SAP GUI
Unified Connectivity (UCONN)
SAP Watchlist Screening
GRC and Security Dashboards
Our SAP Cybersecurity Portfolio Vision
// Supporting the Intelligent, Sustainable Enterprise
// Achieve objectives of the organization more reliably
SAP has a duty of care to all customers to be able to provide solutions to help manage the increasing challenges related to cybersecurity.
SAP provides a broad range of powerful solutions supporting Access Management, Data Protection, Data Privacy and application-level threat and anomaly detection.
Our SAP GRC Security Portfolio
Let’s focus on the SAP GRC Portfolio for cybersecurity, data protection and access governance. These solutions are engineered to assist organizations in safeguarding their digital assets, ensuring the integrity and confidentiality of their data, and managing user access privileges efficiently.
Overall, these solutions deliver a unified perspective of company cybersecurity posture, data protection strategies, and access governance mechanisms. This visibility is crucial in understanding potential vulnerabilities and threats that might impede the achievement of business objectives, enabling leaders to make informed decisions, protect their digital ecosystem, and enhance operations. Moreover, it supports adherence to both internal data governance frameworks and external data protection laws. Below you can see the solution components offered in this domain.
Identity & Access Governance
Cybersecurity, Data Protection and Privacy

Secure Access

Data Protection

Cyber Security
SAP Access Control
SAP UI Data Protection, Masking & Logging
SAP Enterprise Threat Detection
SAP Access Control
SAP Access Control fits into the SAP Governance, Risk, and Compliance solution, and is a powerful security tool for companies using SAP to use. In this video, learn about the SAP Access Control solution and its benefits, management capabilities, segregation of duties, and more.

CIO Guide: Identity Lifecycle in SAP Landscapes
Explore the SAP approach to identity and access management (IAM) in the context of the identity lifecycle.

Enable Centralized, Frictionless Access Control for Business Software and Data
Find out how SAP Access Control helps you take the friction out of application access for employees while incorporating the security checks you need to help protect privacy and data.

SAP Access Control on SAP.COM
Giving employees the applications and services they need without exposing data and processes to unauthorized use.
SAP UI Data Protection, Masking & Logging
Better Data Security with UI logging and field masking from SAP - Learn how UI logging and field masking products from SAP can help your business protect data and minimize the impact of any data breach.
UI Data Protection Masking Product Demo
Demo on 'Level Based Access' Feature. This Solution Demo can be used to show to prospective customers 'Level Based Access' Feature of UI Data Protection Masking product.
UIDP Masking & Logging Overview
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Nunc sit amet mi ut erat suscipit consectetur at vel risus. Quisque posuere sem tellus. Vivamus porttitor et massa non hendrerit.

UI Data Protection L1 Presentation
Overview on the offering of SAP UI Data Protection Masking and Logging.

SAP UI Data Protection Community
Securing access to sensitive personal data is a key requirement of data protection and privacy.
SAP Enterprise Threat Detection
SAP Enterprise Threat Detection - In this video you will see how to protect your business from threats/attackers/others.
In this video SAP, walks you through the key innovations delivered with SAP Enterprise Threat Detection, Cloud Edition.

SAP Enterprise Threat Detection
Helping identify, analyze, and neutralize cyberattacks in your SAP applications as they happen and before serious damage occurs.

The Click Enterprise Threat Detection Forensics Lab
SAP Enterprise Threat Detection Forensics Lab.

Protect the Intelligent Enterprise with SAP Enterprise Threat Detection
The SAP Enterprise Threat Detection application identifies, analyzes, and neutralizes cyberattacks against your SAP solutions and IT environment.
SAP S/4HANA Source-to-Pay Process
What could go wrong?










SAP Identity Access Governance
SAP Data Custodian Key Management
SAP Code Vulnerability Analyzer
SAP Identity Access Governance
See how SAP Cloud Identity Access Governance enables simple, seamless, and adaptive access governance.
SAP Cloud Identity Access Management is our solution to manage the identity lifecyle in hybrid onPremise and cloud landscapes.

CIO Guide: Identity Lifecycle in SAP Landscapes
Explore the SAP approach to identity and access management (IAM) in the context of the identity lifecycle.

SAP Identity Access Governance on SAP.COM
Governing access authorizations with greater ease and minimize mistakes, misuse, and financial loss.
SAP Data Custodian Key Management
Short video demo of SAP Cloud Data Custodian with focus on anomaly detection features.

Supported Application Contexts with SAP Data Custodian KMS
An Application Context is a segregated area in SAP Data Custodian to manage encryption keys for a specific SAP product line.

What is Key Management Service?
SAP Data Custodian Key Management Service provides full key lifecycle management from one SAP service.
SAP Code Vulnerability Analyzer
Learn how you can implement holistic cybersecurity for your SAP systems with Code Vulnerability Analyzer and Solution Manager.

SAP Code Vulnerability Analzer
Overview of SAP Code Vulnerability Analyzer, a static code scanning tool available both in the Cloud and on-premise.

SAP Community Page
SAP Code Vulnerability Analyzer (CVA) is a static code analysis tool that helps you identify and fix security vulnerabilities in your ABAP code. This page provides information on its key features and benefits.
SAP Secure Login Service for SAP GUI
Unified Connectivity (UCON)
SAP Secure Login Service for SAP GUI
Each month, we select and highlight security topics relevant to SAP customers. In March, we will talk about the SAP Secure Login Service for SAP GUI. It is SAP’s new solution for secure authentication and single sign-on for SAP GUI clients. It integrates with your existing identity provider, such as Microsoft Entra ID, thus eliminating the need for multiple passwords, increasing end-user productivity, and protecting business data with strong authentication methods. SAP Secure Login Service for SAP GUI is a cloud offering without on-premise server components, which further simplifies the introduction and reduces TCO.

Identity Lifecycle in SAP Landscapes
Explore the SAP approach to identity and access management (IAM) in the context of the identity lifecycle.

Stronger Authentication and Easier System Access with SAP GUI
Learn how you can use SAP Secure Login Service for SAP GUI to delight your employees by providing user-friendly access to your SAP software systems, simplifying your employees’ daily work, and achieving sustainable cost advantages in IT support.

SAP Secure Login Service for SAP GUI
Everyone wants to work in a productive, secure environment. Give your people that experience with a single sign-on (SSO) service.
Unified Connectivity (UCON)
Three Lines: SAP Audit Management - SAP Audit Management is integrated with SAP S/4HANA as part of the three lines so that your audit is tightly coupled to your day to day operations. You will increase efficiency with automated scans through the integration with Process Control and Business Integrity Screening which comb through data in realtime with remarkable accuracy.

How-To Video Guides for More RFC Security with Unified Connectivity (UCON)
This series of short videos explains how to setup UCON in three steps and guides you through the three-phased UCON Tool to achieve more RFC security in your system landscape.

SAP Unified Connectivity (UCON) documentation
To help you keep up with ever-growing security challenges, SAP NetWeaver 7.40 includes a new framework, Unified Connectivity (UCON), for securing Remote Function Calls (RFCs).

UCON RFC Basic Scenario - Guide to Setup and Operations
To help you keep up with ever-growing security challenges, SAP NetWeaver 7.40 includes a new framework, Unified Connectivity (UCON), for securing Remote Function Calls (RFCs) in ABAP-based systems.
GRC and Security Dashboards
GRC and Security Dashboards
Cyber risks should be managed at the enterprise level with business context. The SAP Digital Boardroom helps provide the visibility and continuity to highlight the linkage between the activities and objectives, and support key discussions when decisions must be taken to allocate resources and fine tune priorities for GRC and Security.
Tied to Objectives
- Risk management framework aligned with business value drivers
- One view of business objectives linked to related risks, controls, and issues
Increased Accountability
- Clear lines of responsibility across operations, risk and compliance management, and internal audit
- Support for an integrated three lines of defense approach
Improved Alignment
- Risk-based approach to reduce unneeded effort for controls and audits
- Focused collaboration to leverage expert knowledge and improve decision making
SAP Cybersecurity Dashboard: Drill-down into Overall Residual Risk
A quick look at a drill-down into the country's Residual Risk related to cyber.
SAP Video - SAP Security Webcast
Join us to discover the new 5 pillars of the SAP GRC solutions portfolio, enabling an orchestrated GRC strategy to face today's complex business environment, siloed processes, unclear accountability, as well as new risks and regulations.
SAP Solutions for Operations and Monitoring
Implement and operate intelligent cloud and hybrid business solutions
SAP propose 2 complementary approaches to build, run, and optimize your intelligent enterprise:
Available for free with all SAP Cloud Solutions subscriptions
- Business Process Monitoring
- Integration & Exception Monitoring
- Real User Monitoring
- Synthetic User Monitoring
- Job & Automation Monitoring
- Landscape Management
- External API Management
- Configuration & Security Analysis
- Health Monitoring
- Business Service Management
- Intelligent Event Processing
- Operations Automation
To be considered for customer with large scale SAP landscape (40+ instances) with advanced needs in system management, user and integration monitoring, and configuration and security analytics.

Requires specific subscription
- Optimized for high-volume system and application monitoring use cases using the full power of SAP HANA
- Maximum automation during the complete life-cycle of systems from onboarding to decommissioning
- Integration & User Monitoring
- Application & System Monitoring
- Alert & Notification Management
- Configuration and Security Analytics
- Analytics & Intelligence
- Root Cause Analysis
- Operations Automation
- Maintenance & Service
- Service Level Management
SAP Security is a Team Sport
Don't forget that SAP security is a team sport. Whatever your landscape is on premise, hybrid, cloud focused, whatever your industry sector SAP provides solutions to cover the core element of your security and compliance program.
We also work on extended scope to cover whatever challenges SAP security and compliance perspective can occur, and we integrate with a number of third-party applications to extend and expand our capacities.
The Approach and Outcome
The five phases can be broken down to detailed activities
⍟ Analyze business & digital strategy, operating model, organization, and vision*
⍟ Analyze business model & organization
⍟ Analyze as-is enterprise architecture
⍟ Create as-is system list
⍟ Run Process Discovery (Readiness Check)
⍟ Define life science to-be business processes
⍟ Identify IT applications and innovations
⍟ Design target life science application architecture
⍟ Integrate life science architecture into overall IT landscape
⍟ Define transformation roadmap
⍟ Define roll-out plan
⍟ Define & evaluate Implementation Strategy
⍟ Conduct risk assessment
⍟ Conduct change impact analysis
⍟ Estimate costs, quantify value, calculate business case
⍟ Provide transformation guidance
⍟ Provide approach, policies, principles, standards, key success factors
⍟ Implementation program organization, roles & responsibilities
Typical project plan showing main service phases
Service Preparation Phase
~1-3 Weeks
✪ Prepare for service delivery (refine scope and approach, service schedule and deliverables)
✪ Mobilize SAP consultants and customer stakeholders
✪ Prepare and execute kick-off meeting
✪ Confirm final scope and schedule service delivery workshops
Service Delivery Phase
~16-48 Weeks
✪ Perform activities as required (such as workshops, interviews, design, planning, justification, evaluation and documentation) for building blocks
- Discover
- Design
- Plan
- Justify*
- Transform and scale*
✪ Manage project (performed on a permanent basis as required during the execution of the service)
* Scope option Extended only
Service Closure Phase
~1-2 Weeks
✪ Complete service documentation
✪ Perform final presentation: Present and discuss results, propose follow-up activities and next steps
✪ Hand over deliverables, and close service
The Analysts View
Most comprehensive solution improved with the collaboration of our partners and customers
SAP Recognized by Chartis Research as a Leader in Governance, Risk, and Compliance
“SAP’s category-leading position in our iGRC quadrants reflects its strong set of solutions across most of the major GRC categories,” said Sid Dash, chief research at Chartis. “Moreover, it combines these with a strong element of integration, as well as links with corporate operations and infrastructure management.”
Learn from leading customers how SAP added value

~75%
Reduction in time-to-report compared to traditional siloed GRC
Trillions
of data records analyzed every day
10000+
customers in 180 countries
QUALIFICATION SURVEY
20+
years helping companies in managing risks
Extensive
coverage of the most critical risks with specialized solutions
QUALIFICATION SURVEY
90%
90% improvement in visibility with 15% reduction in risk and loss events
The Approach and Outcome
The five phases can be broken down to detailed activities
⍟ Analyze business & digital strategy, operating model, organization, and vision*
⍟ Analyze business model & organization
⍟ Analyze as-is enterprise architecture
⍟ Create as-is system list
⍟ Run Process Discovery (Readiness Check)
⍟ Define life science to-be business processes
⍟ Identify IT applications and innovations
⍟ Design target life science application architecture
⍟ Integrate life science architecture into overall IT landscape
⍟ Define transformation roadmap
⍟ Define roll-out plan
⍟ Define & evaluate Implementation Strategy
⍟ Conduct risk assessment
⍟ Conduct change impact analysis
⍟ Estimate costs, quantify value, calculate business case
⍟ Provide transformation guidance
⍟ Provide approach, policies, principles, standards, key success factors
⍟ Implementation program organization, roles & responsibilities
Typical project plan showing main service phases
Service Preparation Phase
~1-3 Weeks
✪ Prepare for service delivery (refine scope and approach, service schedule and deliverables)
✪ Mobilize SAP consultants and customer stakeholders
✪ Prepare and execute kick-off meeting
✪ Confirm final scope and schedule service delivery workshops
Service Delivery Phase
~16-48 Weeks
✪ Perform activities as required (such as workshops, interviews, design, planning, justification, evaluation and documentation) for building blocks
- Discover
- Design
- Plan
- Justify*
- Transform and scale*
✪ Manage project (performed on a permanent basis as required during the execution of the service)
* Scope option Extended only
Service Closure Phase
~1-2 Weeks
✪ Complete service documentation
✪ Perform final presentation: Present and discuss results, propose follow-up activities and next steps
✪ Hand over deliverables, and close service

Secure Access

Data Protection

Cyber Security
Additional Information
SAP protects businesses’ applications and data by building, running, and maintaining more-secure operations.

Enterprise Risk, Controls & Compliance and Audit (Three Lines)
See how SAP GRC Solutions helps you improve compliance, optimize audit resource utilization, and mitigate risk more efficiently in SAP S/4HANA.

Identity and Access Governance
Learn how SAP Cloud Identity Access Governance enables simple, seamless, and adaptive access governance.

Cyber Security
Security solutions from SAP support data protection, cybersecurity, and business resiliency for companies running SAP solutions and services.
Reach out to rethink your Governance, Risk & Compliance Journey with SAP
Please feel free to contact us for more information about our portfolio, but also to start a dialogue about your specific use-cases and to better define the challenge. Given fast-changing and ever-complexing nature of your business, we are looking to merge your deep expertise with our modern tools and technologies to better understand the challenge and work together toward the future.
Your SAP Team
Please feel free to contact us for more information about our portfolio, but also to start a dialogue about your specific use-cases and to better define the challenge. Given fast-changing and ever-complexing nature of your business, we are looking to merge your deep expertise with our modern tools and technologies to better understand the challenge and work together toward the future.
Andrei Nifatov
Emerging Africa | Oman | Qatar | Jordan | Lebanon | Southern Africa | South Africa | UAE
Farhan Ashfaq
Emerging Africa | Oman | Qatar | Jordan | Lebanon | Southern Africa | South Africa | UAE